Red Hat Enterprise Linux
Everywhere enterprise IT is headed, Red Hat® Enterprise Linux® is there. From the public cloud to the edge, it evolves to bring flexibility and reliability to new frontiers. This is the stable foundation for untold innovation.
The value of Red Hat Enterprise Linux
Red Hat Enterprise Linux is the world’s leading enterprise Linux platform,* certified on hundreds of clouds and with thousands of hardware and software vendors.
Features and benefits
Red Hat Enterprise Linux can be purchased to support specific use cases like edge computing or SAP workloads, but every subscription includes these core benefits:
Subscription benefits
Red Hat Enterprise Linux provides more than an operating system—it also connects you to Red Hat’s extensive hardware, software, and cloud partner ecosystem, and comes with 24x7 support. Red Hat Enterprise Linux 9.3 is our latest release, but with access to all supported versions and a 10 year life cycle, you can upgrade on your schedule and adopt new features when needed.
Supported architectures
Red Hat Enterprise Linux can be optimized to run on servers or high-performance workstations, and supports a range of hardware architectures like x86, ARM, IBM Power, IBM Z, and IBM LinuxONE. Our deep collaboration with upstream communities and hardware partners makes this possible, bringing you a reliable platform for many use cases and a consistent application environment across physical, virtual, and cloud deployments.
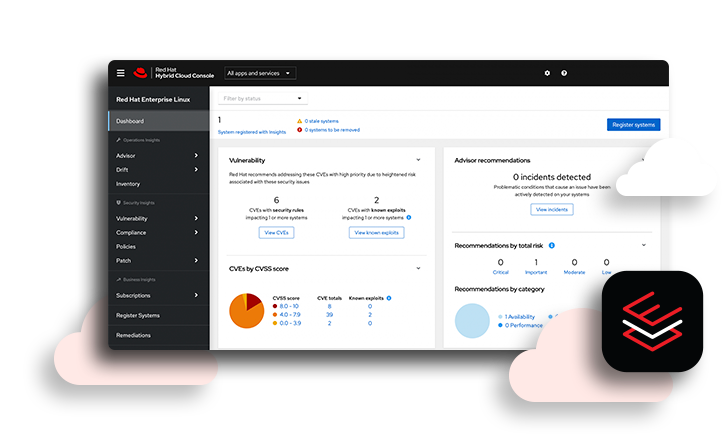
Automation and management
Get a consistent and stable administrative experience, allowing admins to spend more time on innovation—less time on repetitive, error-prone tasks. Red Hat Enterprise Linux includes Red Hat Insights, a managed service for analytics and remediation that delivers continuous vulnerability alerts and targeted guidance to help organizations maximize uptime and avoid emergencies. Plus, with the Red Hat Satellite add-on you can automate the remediation process.
Install and migration tools
From your first steps installing, migrating, or upgrading Red Hat Enterprise Linux to eventually deploying across multiple clouds, we provide utilities to help. Our migration tools make it easy to get started if you’re coming from CentOS Linux or another distro, and you can create optimized operating system images with Red Hat Enterprise Linux image builder that can handle the details of cloud deployments when you’re ready.
Security and compliance
Simplify how your organization mitigates risk, automates security, and maintains compliance. Red Hat Enterprise Linux includes built-in security features like live kernel patching, security profiles, security standards certification, and a trusted software supply chain to help meet today’s high security and compliance expectations.
Consistent performance
No matter what hardware or workloads you are running, our comprehensive performance monitoring, tracing, and analysis tools help you optimize your systems. Detect performance anomalies, build a comprehensive view of system performance, and apply best-practices through preset tuning profiles so you can get the most out of your investments.
A direct migration path for CentOS Linux 7 users
On June 30, 2024, CentOS Linux 7 will reach End of Life (EOL). Red Hat® Enterprise Linux® is a fully supported production-grade operating system (OS) available on premises and in the cloud–and it’s a direct migration path for CentOS Linux users.
Whether you’re using only CentOS Linux or are an existing Red Hat Enterprise Linux customer, and also have CentOS Linux, we have a streamlined migration solution for your needs.
Our Convert2RHEL tool streamlines the migration process by minimizing the need for costly redeployment projects and reduces administrative burden by maintaining existing OS customizations, configurations, and preferences during the conversion.
Red Hat Enterprise Linux for Third Party Linux Migration is a competitively-priced offering that includes access to Red Hat Enterprise Linux 7, tooling to convert in-place instances of CentOS Linux 7 to Red Hat Enterprise Linux 7, and patches and upgrades for an additional 4 years after the EOL date. It is available on the AWS Marketplace and Azure Marketplace, and will also be available on Google Cloud soon.
Whether you’re using only CentOS Linux or are an existing Red Hat Enterprise Linux customer, and also have CentOS Linux, we have a streamlined migration solution for your needs.
Customer story
Salesforce transitions from CentOS Linux to Red Hat Enterprise Linux 9
The company is migrating over 200,000 systems to streamline IT operations and enhance customer experiences.
The ideal OS on the cloud
Position your organization for success with a flexible, optimized OS built to respond to rapid change. Red Hat Enterprise Linux works seamlessly with leading cloud providers to deliver superior security, workload migration, and tools for management and visibility—giving you a clear path from development to production.
Red Hat Enterprise Linux
on AWS
- Gives AWS customers a powerful, adaptable innovation platform certified to work seamlessly with Amazon's cloud infrastructure.
- Allows your organization to scale in any direction with Amazon's globally available, on-demand compute capacity.
Red Hat Enterprise Linux
on Azure
- Offers Azure customers tested and certified interoperability for on-premise and cloud-based applications.
- Protects your data with security controls, upgrades, and patches, as well as integrated features to help you stay compliant across your hybrid environment.
- Access the Forrester report to find how Red Hat Enterprise Linux on Azure drives significant ROI and operational benefits.
Red Hat Enterprise Linux
on Google Cloud
- Helps Google Cloud customers simplify cloud migrations and increase time to value with a consistent set of management tools.
- Delivers faster queries and analytics on SAP-certified Google Cloud instances.
Use cases for any cloud, any workload
Expand to the edge
Red Hat Enterprise Linux extends your hybrid cloud infrastructure to the edge, scaled across hundreds—or even hundreds of thousands—of nodes all over the world. Create edge-optimized OS images, minimize workload interruptions caused by OS updates, transfer system updates more efficiently, and have confidence in automatic health checks and rollbacks.
Hybrid cloud starts with Linux
Red Hat Enterprise Linux enables you to deploy and run applications anywhere—from physical and virtual, to private and public clouds—by delivering the consistent operating foundation needed for modern IT and enterprise hybrid cloud deployments. As the 2023 Google Cloud Partner of the Year, the way we work with major cloud providers isn’t just robust—it's award-winning. We also collaborate with AWS, Microsoft Azure, and Oracle Cloud Infrastructure (OCI), which means customers can support future-focused deployments on the solid foundation of Red Hat Enterprise Linux.
Migrate SAP workloads
Organizations that depend on SAP to manage their business need an operating system that delivers performance, reliability, and the ability to modernize and integrate their SAP and non-SAP applications. With Red Hat Enterprise Linux for SAP Solutions, organizations can meet these needs and comply with the quickly approaching SAP requirement to migrate their applications to SAP HANA and SAP S/4HANA by the 2027 deadline.
Deliver SQL Server on Linux
Searching for a performance-driven, cost-effective platform for Microsoft SQL Server? Red Hat Enterprise Linux provides a scalable foundation and a consistent application experience across bare-metal, virtual machine, container, and hybrid cloud environments.
Developing on Red Hat Enterprise Linux
Developers who join the Red Hat Developer program get access to Red Hat Enterprise Linux, how-to videos, demos, "get started" guides, documentation, and more. We offer a vast ecosystem to help you build and deploy apps in the cloud and our Universal Base Image (UBI) provides a solid and stable Red Hat Enterprise Linux userspace to streamline efforts as you expand into container development projects.
Scale your HPC workloads with Red Hat Enterprise Linux
Your operating system plays a key role in determining how well your high performance computing (HPC) infrastructure operates and performs. It connects your hardware, software, networking, and interfaces to form a unified, orchestrated environment. Red Hat Enterprise Linux provides a flexible and reliable platform for running HPC workloads at scale across datacenter, cloud, and hybrid environments.
Open hybrid cloud
A shared technological foundation
Red Hat’s open hybrid cloud strategy is built on the technological foundation of Linux®, containers, and automation. An open hybrid cloud approach gives you the flexibility to run your applications anywhere you need them.

Red Hat Ansible Automation Platform lets you automate compliance and gain consistency across your Red Hat Enterprise Linux environments.

Red Hat Enterprise Linux is the proven foundation for Red Hat OpenShift, certified on thousands of hardware and cloud vendor technologies. This means the security, performance, interoperability, and innovation of Red Hat Enterprise Linux is extended throughout your infrastructure to provide a single platform that can run wherever you need it.

Every technology within your IT stack needs to work well together. Because those connections rely on the operating system, it has to be consistent, reliable, and flexible. Red Hat Enterprise Linux is the common link connecting modern IT.
How our customers use Red Hat Enterprise Linux
UPS created a container-based application platform that enables developers to more efficiently create new features for operations logistics and staffing.
Lufthansa Technik used hybrid cloud infrastructure to build a digital platform that uses data to better organize and schedule airline maintenance.
Tomago Aluminium improved development efficiency, consolidated its server footprint, and enhanced system and data security by migrating its SAP solution.
If you’re looking for Linux, I don’t think that there’s a better-supported solution than RHEL.
Training and certification
Try our learning subscription
Get limited, self-service access to select labs and courses with a free 14-day trial of Red Hat Learning Subscription.
Featured news
Get ready for Red Hat Enterprise Linux 7 End of Maintenance
Red Hat Enterprise Linux 7 will reach End of Maintenance on June 30, 2024. If you are a current Red Hat Enterprise Linux customer, upgrade now to supported versions of Red Hat Enterprise Linux 8 or 9 to take advantage of new features, security enhancements, bug fixes, cloud functionality, and more.
Red Hat Enterprise Linux 8.10 and 9.4 Beta released
Red Hat is pleased to announce the release of Red Hat Enterprise Linux 8.10 and 9.4 Beta, with new features and enhancements to help you deliver workloads, applications, and services with increased efficiency and agility across multiple environments.
Red Hat named a Google Cloud Technology Partner of the Year
At the recent Google Cloud Next conference, Red Hat was recognized as a 2023 Google Cloud Technology Partner of the Year (Infrastructure - Compute). Take a closer look at how the two companies collaborate to help customers embrace hybrid cloud strategies.